If someone hacked into your bank account, you would know that they were after your money. If they hacked into your email account, though, you need to think of what they wanted with your email.
Perhaps they wish to pretend to be you and ask your relatives for money. Perhaps they want to see if they could write to your bank to have your passwords changed (banks will often entertain password requests if they come from the registered email account).
Sometimes, victims find that hackers have gone in and changed the default shipping address on their online shopping accounts. They only learn about this when they place an order and it goes to the hacker’s address. You need to think about what exactly your hackers might have found of value and head them off before they do real harm.
With this in mind, everyone worries about having his or her computer infected, identity stolen or online account hacked, right? Sadly this is not true and they only worry after its already happened. Many look for someone else to blame but the reality is that that there are simple steps you can take to greatly reduce the chances of these bad things happening to you.
1- Create strong, secure, unique passwords for everything
The harm created by data breaches is magnified because too many people use weak passwords and/or use the same password for more than one online account. Because of that, a single breach can lead to break-ins at many more services. Avoid this fate by creating strong, secure passwords for every account, and not reusing those passwords for other accounts.
Enable two-factor authentication on every account where possible. Two-factor authentication (2FA) will prevent an online account from being hijacked, even if a hacker knows your password. Without a PIN sent to your smartphone, he or she won’t be able to get in. Apple, Microsoft, Google, Facebook, LinkedIn, Twitter, Dropbox and dozens of other services allow 2FA — enable it now.
Passwords today need to be so long and complicated that you can’t possibly remember them all. Let a password manager do the remembering for you. Some of these programs store your passwords online, while other keep them on your computer or phone, but all protect the password “vault” with strong encryption. All you need to remember is a single master password.
2- Secure your PC and notebook
This is the single most important tip here. Far too many hacks occur because someone hasn’t updated Windows or Internet Explorer. Make sure Windows, macOS and iOS are always up-to-date with the latest patches, and that any applications that face the internet, such as web browsers and email clients, are also updated.
If a product is no longer supported, such as Windows XP or Internet Explorer versions 6 through 10, then upgrade to a newer version. If your device is too old to receive the latest updates, it’s time for a new device. (Caveat: Many Android users can’t update to the latest version of Android, because their device makers or wireless carriers won’t let them.)
Encrypting part or all of your storage drive will protect it from anyone who wants to examine your device without your permission. iOS encrypts a device as soon as a PIN or passcode is set up, and macOS’ File Vault and Android’s encryption tool are easy to enable.
With Windows, it’s more complicated. The Pro, Enterprise and Ultimate editions of Vista through 10 come with the excellent BitLocker encryption tool. Windows 10 has a separate built-in encryption tool for all editions, but it doesn’t work on every computer. You might want to try a third-party tool instead, such as TrueCrypt or VeraCrypt.
Disable Flash or make it click-to-run as Adobe Flash Player is the web’s worst habit. It’s always being hacked, yet everyone continues to run it. Break from the herd: Disable Adobe Flash Player so that it doesn’t run at all (Safari’s default setting has no Flash), or make it click-to-run so that it only loads when you let it.
Keep all your applications and your operating system patched and updated at all times and make sure you update you have antivirus/internet security software running at all times. Oh, and make sure you update your antivirus/internet security software daily.
3 – Secure your phone and tablet too
Your smartphone logs right into your email and social-media accounts, your home Wi-Fi network, and possibly even your online bank account. It’s got the names, numbers and email addresses of all your friends and family. You don’t want some random person who picks up your phone to get all that information, do you? Lock your phone’s screen and use the most complex method such as a six-digit PIN or an alphanumeric password.
There’s no quicker way to get your Android device infected than by installing apps from outside the official Google Play app store. Apps available in “off-road” markets are frequently pirated and/or infected.
You already know that Windows machines need antivirus software, but did you know that Mac, Android devices and Linux boxes do too? Antivirus software may (or may not) slow down your machine a bit, but it will give you a strong line of defence against malware, phishing schemes and other threats from the internet or from USB devices. (We would recommend AV software for iOS devices as well, but Apple doesn’t permit it.)
4 – Secure your online accounts
Once again, passwords today need to be so long and complicated that you can’t possibly remember them all. Let a password manager create a complex password for you and use that. All you need to remember is a single master password.
There are several online third-party services that do this including LastPass, DashLane, and 1Password. They store passwords in the cloud and secure them all with a master password. If entrusting all your passwords to the cloud gives you the creeps, consider using a local password storage program on your computer, such as Roboform, PasswordSafe or Keepass. Again, take care to pick a strong master password, but one that you can remember; just as with the Firefox master password option, if you forget the master password you are pretty much out of luck.
Whatever you do, don’t store your list of passwords on your computer in plain text and avoid using the same password at multiple Web sites.
Scan all email attachments – Infected email attachments can carry spyware, ransom-ware, malware or all sort of other digital issues. Even if you’re expecting an attachment, it’s best to scan it with your antivirus software. Some AV software lets you scan attachments right in the body of the email; in other cases, you’ll have to save the attachment to a designated folder and then right-click the file to manually scan it.
5 – Secure your online websites
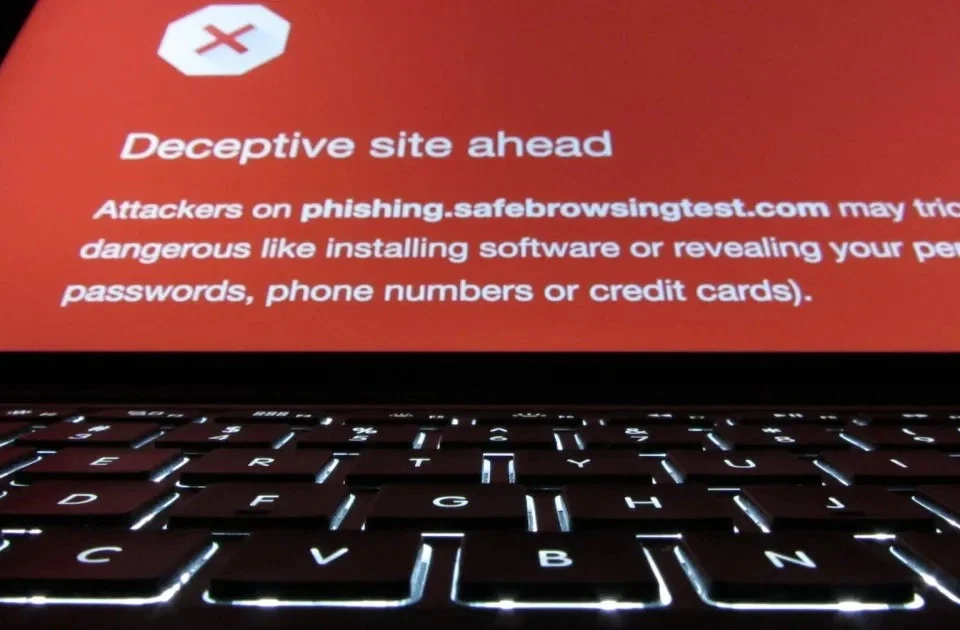
You may not think your site has anything worth being hacked for, but websites are compromised all the time. The majority of website security breaches are used to steal your identity, steal your data or use your website as an email relay for malware, ransom-ware and spam and to serve files of an illegal nature.
Hacking is regularly performed by automated scripts written to scour the Internet in an attempt to exploit known website security issues in software.
Keep all software up to date – It may seem obvious, but ensuring you keep all software up to date is vital in keeping your site secure. If you are using third-party software on your website such as a WordPress, Joomla and Drupal, you should ensure you are quick to apply any security patches. Most vendors have a mailing list or RSS feed detailing any website security issues. The WordPress team work hard to creates patches to help fix security holes so benefit from their hard work. Check the official WordPress site for the latest version here and remember this applies to all WordPress Plugins and themes.
When website security holes are found in software, hackers are quick to attempt to abuse them so applying software updates needs to happen as frequently as possible. Hackers don’t go on holidays so your site is vulnerable if you are not frequently updating it. Best practice is to perform checks for updates on a daily basis.
If you are using a managed hosting solution or have website maintenance then you don’t need to worry so much about applying security updates for the operating system as the hosting company should take care of this.
Don’t fall for the Unlimited Hosting trick – Yes we understand the temptation and it is cheaper on your pocket choosing the ‘unlimited’ hosting plans. The use of the word unlimited is generally used by hosting companies to attract your attention and then to keep prices low they put as many websites as they possibly can on a single server. Its like offering cheap airline tickets where safety is disregarded and you jam in as many people as you can shoulder to shoulder. In terms of security, the experts would say it ‘creates a very large attack surface’. This basically means it offers hackers many more ways to break in to your sites. If the hacker can then get into one of the sites he can take over all of your sites on that same server.
Don’t use domain addons – Again, why have several hosting accounts when you can host them all under the one account by using domain addons. Its cheaper right? For example, on a unlimited package you have might have placed 10 or your websites. The hacker can use this weakest link to break into that one sites and have full and complete access to take over your other 9 websites. With their tools they usually have a lot more access than you have with your WordPress admin console.
If your website is important to you invest some money and get is hosted with a company that does not offer unlimited everything.
Backup your site – Unless you are an up and coming security expert and can spare the time each day to keep your site fully watched then backup your site. This is even more important if you try to fix your website yourself if it is hacked. That could be your first time at cleaning a website which means a good chance of breaking your website. Backup all the files of your website and do a full database backup. Stores these files on a different server than your current website.
6 – Secure your router
This is a bit technical, but very important. Dig out your home Wi-Fi router’s instruction manual and learn how to check for and install new firmware.
Firmware is your router’s operating system, and needs to be periodically updated to fix security flaws. If a hacker manages to take control of your router, he can control everything you do online, from sending email to posting on Facebook to sending money to other online bank accounts.
Your Wi-Fi router will come with a default administrative username and password, but far too many people don’t change these after setting up the routers. Hackers have lists of default router admin credentials, and use them to remotely access and hijack home networks. Avoid this fate by referring to the instruction manual and creating a unique username and password for your router’s admin account.
Change your Wi-Fi network name and select WPA2 encryption for Wi-Fi