You may have read about an unprecedented cyberattack involving the ‘Carbanak’ cybergang.
Since 2013, they have stolen up to one billion dollars from more than 100 banks and financial institutions in at least 30 countries, including Australia. Losses per bank range from $2.5 million to approximately $10 million, making this the most successful criminal cyberrobbery to date. These attacks still remain active.
The starting point of this attack doesn’t seem highly-sophisticated. The cybercriminals gained entry into an employee’s computer with a spear phishing^ email infecting the employees PC with the ‘Carbanak’ malware.
According to Kaspersky Lab ‘they were then able to jump into the internal network and track down administrators’ computers for video surveillance. This allowed them to see and record everything that happened on the screens of staff who serviced the cash transfer systems. In this way the fraudsters got to know every last detail of the bank clerks’ work and were able to mimic staff activity in order to transfer money and cash out.”
All of us need to look after our own security procedures and strive to block all phishing emails before they even reach the end user.
Rigorous security training for all employees, not just the IT team, is vital. Only with employee training and strong security solutions can companies hope to ensure their employees and employee information doesn’t become a weapon for the cyber criminals.
What impact would it have on your business if your network and systems became compromised?
Security is best done with a layered approach
No product is going to secure your network 100%. The risk of something getting through will always be there but you can reduce these as much as possible with a layered approach.
Those layers include:
- Offsite Spam filtering – Ideally with Anti Virus built in, such as JAMF
- Anti Virus at the firewall
- Anti Virus at the email gateway
- Anti Virus at the desktop/server
- Following best practices for good password management
- No open shares or other network services
- Monitor all accounts, network activity, groups, etc.
And it goes without saying – DO NOT open suspicious emails, especially if they have an attachment!
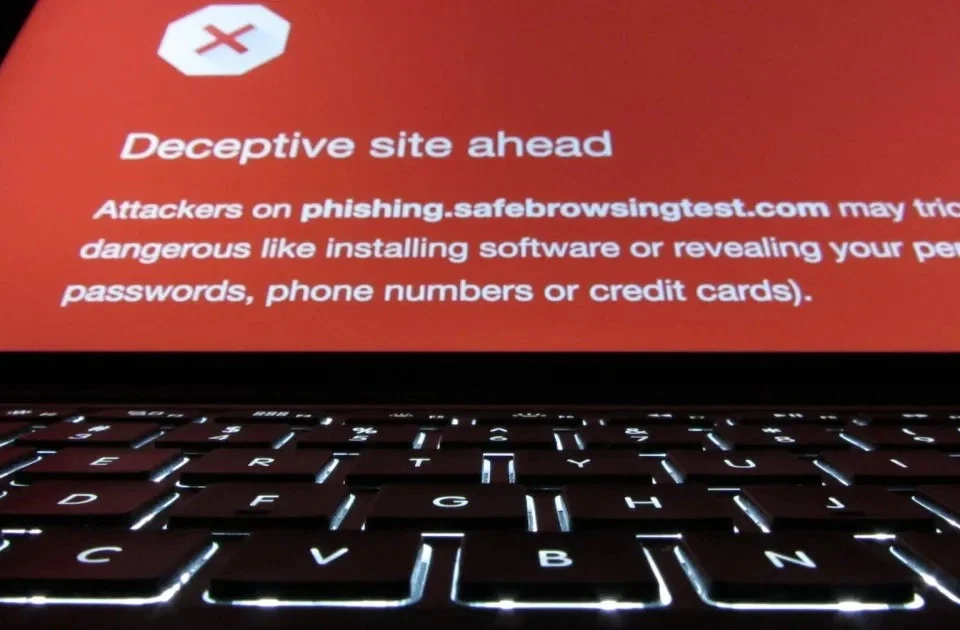
In a spear phishing attack, hackers use email messages to trick people into providing sensitive information, click on links, or download malware. It is a targeted email scam which hones in on specific individual or company. The emails are seemingly sent from organizations or individuals the potential victims would normally get emails from, making them even more deceptive. The intent is to gain remote control and steal intellectual property and other confidential data. This technique is, by far, the most successful on the internet today.